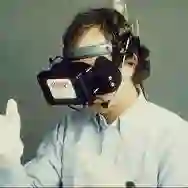
Various industries have widely adopted Virtual Reality (VR) and Augmented Reality (AR) technologies to enhance productivity and user experiences. However, their integration introduces significant security challenges. This systematic literature review focuses on identifying devices used in AR and VR technologies and specifies the associated vulnerabilities, particularly during the reconnaissance phase and vulnerability assessment, which are critical steps in penetration testing. Following Kitchenham and Charters' guidelines, we systematically selected and analyzed primary studies. The reconnaissance phase involves gathering detailed information about AR and VR systems to identify potential attack vectors. In the vulnerability assessment phase, these vectors are analyzed to pinpoint weaknesses that malicious actors could exploit. Our findings reveal that AR and VR devices, such as headsets (e.g., HTC Vive, Oculus Quest), development platforms (e.g., Unity Framework, Google Cardboard SDK), and applications (e.g., Bigscreen VR, VRChat), are susceptible to various attacks, including remote code execution, cross-site scripting (XSS), eavesdropping, and man-in-the-room attacks. Specifically, the Bigscreen VR application exhibited severe vulnerabilities like remote code execution (RCE) via the 'Application.OpenURL' API, XSS in user inputs, and botnet propagation. Similarly, the Oculus Quest demonstrated susceptibility to side-channel attacks and ransomware. This paper provides a detailed overview of specific device vulnerabilities and emphasizes the importance of the initial steps in penetration testing to identify security weaknesses in AR and VR systems. By highlighting these vulnerabilities, we aim to assist researchers in exploring and mitigating these security challenges, ensuring the safe deployment and use of AR and VR technologies across various sectors.
翻译:虚拟现实(VR)与增强现实(AR)技术已在众多行业中得到广泛应用,以提升生产力与用户体验。然而,其集成应用也带来了显著的安全挑战。本系统性文献综述聚焦于识别AR与VR技术中使用的设备,并详细阐述相关漏洞,特别是在渗透测试关键步骤——侦察阶段与漏洞评估阶段。遵循Kitchenham与Charters的指南,我们系统性地筛选并分析了主要研究。侦察阶段涉及收集AR与VR系统的详细信息,以识别潜在的攻击向量;漏洞评估阶段则对这些向量进行分析,以定位恶意行为者可能利用的弱点。我们的研究发现,AR与VR设备——如头戴式显示器(例如HTC Vive、Oculus Quest)、开发平台(例如Unity Framework、Google Cardboard SDK)以及应用程序(例如Bigscreen VR、VRChat)——易受多种攻击影响,包括远程代码执行、跨站脚本攻击(XSS)、窃听及“房间内中间人”攻击。具体而言,Bigscreen VR应用暴露出严重漏洞,如通过'Application.OpenURL' API实现的远程代码执行(RCE)、用户输入中的XSS漏洞以及僵尸网络传播。同样,Oculus Quest亦被证实易受侧信道攻击与勒索软件侵害。本文详细概述了特定设备的漏洞,并强调了渗透测试初始步骤对于识别AR与VR系统安全弱点的重要性。通过揭示这些漏洞,我们旨在帮助研究者探索并缓解这些安全挑战,确保AR与VR技术在各领域的安全部署与使用。