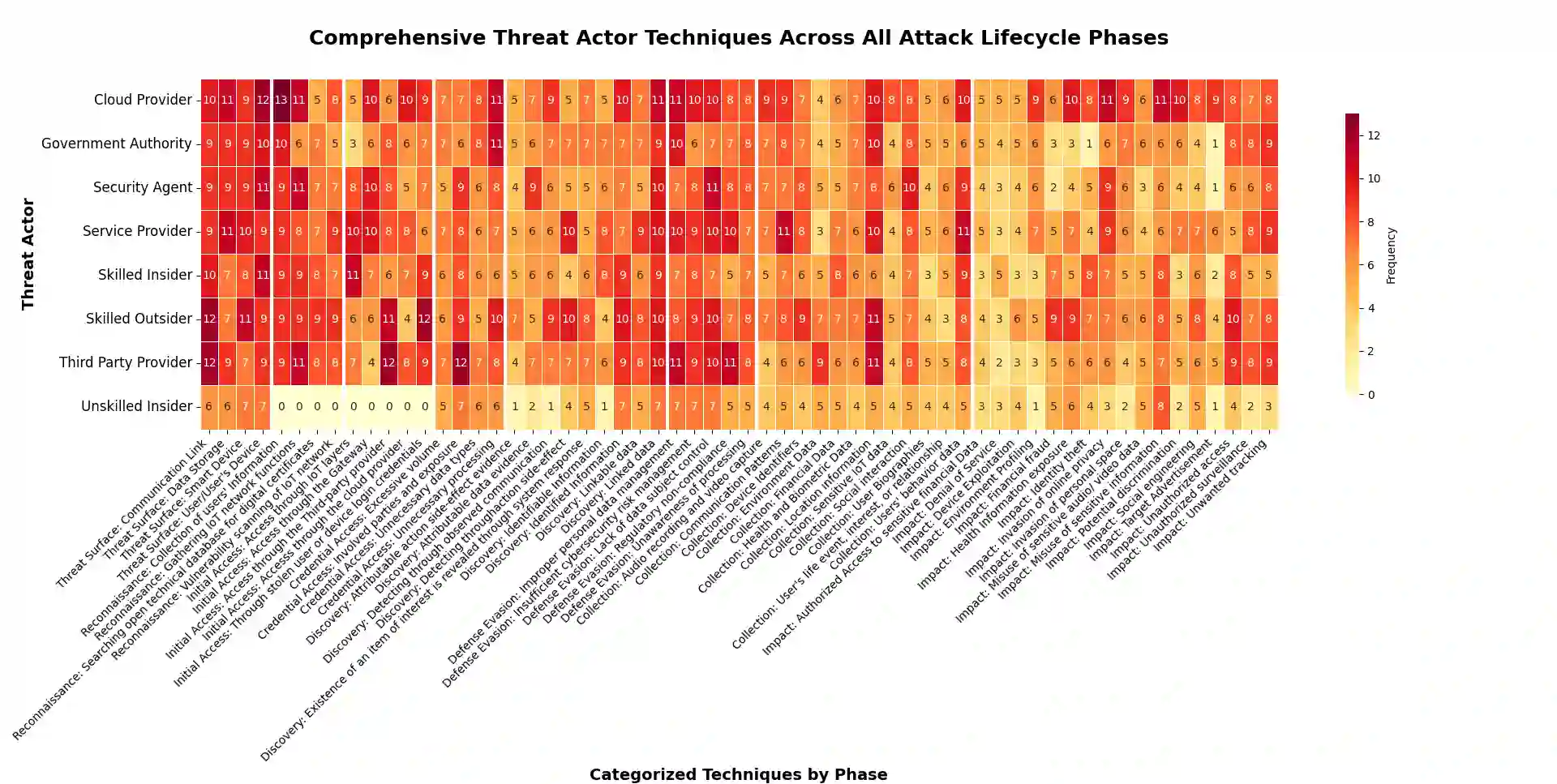
Previous studies on PTA have focused on analyzing privacy threats based on the potential areas of occurrence and their likelihood of occurrence. However, an in-depth understanding of the threat actors involved, their actions, and the intentions that result in privacy threats is essential. In this paper, we present a novel Privacy Threat Model Framework (PTMF) that analyzes privacy threats through different phases. The PTMF development is motivated through the selected tactics from the MITRE ATT\&CK framework and techniques from the LINDDUN privacy threat model, making PTMF a privacy-centered framework. The proposed PTMF can be employed in various ways, including analyzing the activities of threat actors during privacy threats and assessing privacy risks in IoT systems, among others. In this paper, we conducted a user study on 12 privacy threats associated with IoT by developing a questionnaire based on PTMF and recruited experts from both industry and academia in the fields of security and privacy to gather their opinions. The collected data were analyzed and mapped to identify the threat actors involved in the identification of IoT users (IU) and the remaining 11 privacy threats. Our observation revealed the top three threat actors and the critical paths they used during the IU privacy threat, as well as the remaining 11 privacy threats. This study could provide a solid foundation for understanding how and where privacy measures can be proactively and effectively deployed in IoT systems to mitigate privacy threats based on the activities and intentions of threat actors within these systems.
翻译:先前关于隐私威胁分析(PTA)的研究主要集中于基于潜在发生区域及其发生可能性来分析隐私威胁。然而,深入理解所涉及的威胁行为者、其行动以及导致隐私威胁的意图至关重要。本文提出了一种新颖的隐私威胁模型框架(PTMF),该框架通过不同阶段分析隐私威胁。PTMF的开发借鉴了MITRE ATT&CK框架中的选定战术以及LINDDUN隐私威胁模型中的技术,使得PTMF成为一个以隐私为中心的框架。所提出的PTMF可以多种方式应用,包括分析隐私威胁期间威胁行为者的活动、评估物联网系统中的隐私风险等。在本文中,我们基于PTMF开发了一份问卷,对与物联网相关的12种隐私威胁进行了用户研究,并招募了来自工业界和学术界的隐私与安全领域专家以收集他们的意见。通过分析并映射收集到的数据,我们识别了参与物联网用户识别(IU)以及其余11种隐私威胁的威胁行为者。我们的观察揭示了在IU隐私威胁以及其余11种隐私威胁中,排名前三的威胁行为者及其所使用的关键路径。这项研究为理解如何以及在哪里可以主动且有效地在物联网系统中部署隐私措施以减轻隐私威胁,提供了坚实的基础,这些措施基于威胁行为者在系统内的活动和意图。