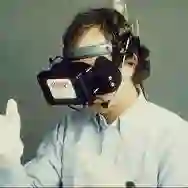
Virtual reality (VR), while enhancing user experiences, introduces significant privacy risks. This paper reveals a novel vulnerability in VR systems that allows attackers to capture VR privacy through obstacles utilizing millimeter-wave (mmWave) signals without physical intrusion and virtual connection with the VR devices. We propose mmSpyVR, a novel attack on VR user's privacy via mmWave radar. The mmSpyVR framework encompasses two main parts: (i) A transfer learning-based feature extraction model to achieve VR feature extraction from mmWave signal. (ii) An attention-based VR privacy spying module to spy VR privacy information from the extracted feature. The mmSpyVR demonstrates the capability to extract critical VR privacy from the mmWave signals that have penetrated through obstacles. We evaluate mmSpyVR through IRB-approved user studies. Across 22 participants engaged in four experimental scenes utilizing VR devices from three different manufacturers, our system achieves an application recognition accuracy of 98.5\% and keystroke recognition accuracy of 92.6\%. This newly discovered vulnerability has implications across various domains, such as cybersecurity, privacy protection, and VR technology development. We also engage with VR manufacturer Meta to discuss and explore potential mitigation strategies. Data and code are publicly available for scrutiny and research at https://github.com/luoyumei1-a/mmSpyVR/
翻译:虚拟现实(VR)在提升用户体验的同时,也带来了显著的隐私风险。本文揭示了一种VR系统中的新型漏洞,该漏洞允许攻击者利用毫米波(mmWave)信号,无需物理入侵或与VR设备建立虚拟连接,即可穿透障碍物捕获VR隐私信息。我们提出了mmSpyVR,一种利用毫米波雷达针对VR用户隐私的新型攻击方法。mmSpyVR框架包含两个主要部分:(i)一个基于迁移学习的特征提取模型,用于从毫米波信号中实现VR特征提取;(ii)一个基于注意力的VR隐私窥探模块,用于从提取的特征中窥探VR隐私信息。mmSpyVR展示了从穿透障碍物的毫米波信号中提取关键VR隐私信息的能力。我们通过机构审查委员会(IRB)批准的用户研究评估了mmSpyVR。在涉及22名参与者、使用三家不同制造商的VR设备进行的四个实验场景中,我们的系统实现了98.5%的应用识别准确率和92.6%的击键识别准确率。这一新发现的漏洞对网络安全、隐私保护和VR技术发展等多个领域具有重要影响。我们还与VR制造商Meta进行了接洽,以讨论和探索潜在的缓解策略。数据和代码已在https://github.com/luoyumei1-a/mmSpyVR/ 公开,供审查和研究使用。