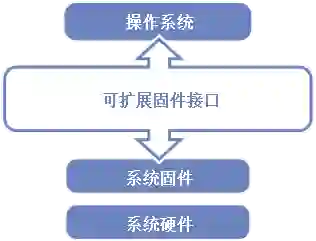
Firmware serves as a foundational software layer in modern computers, initiating as the first code executed on platform hardware, similar in function to a minimal operating system. Defined as a software interface between an operating system and platform firmware, the Unified Extensible Firmware Interface (UEFI) standardizes system initialization and management. A prominent open-source implementation of UEFI, the EFI Development Kit II (EDK2), plays a crucial role in shaping firmware architecture. Despite its widespread adoption, the architecture faces challenges such as limited system resources at early stages and a lack of standard security features. Furthermore, the scarcity of open-source tools specifically designed for firmware analysis emphasizes the need for adaptable, innovative solutions. In this paper, we explore the application of general code audit tools to firmware, with a particular focus on EDK2. Although these tools were not originally designed for firmware analysis, they have proven effective in identifying critical areas for enhancement in firmware security. Our findings, derived from deploying key audit tools on EDK2, categorize these tools based on their methodologies and illustrate their capability to uncover unique firmware attributes, significantly contributing to the understanding and improvement of firmware security.
翻译:固件作为现代计算机的基础软件层,在平台硬件上作为首个执行的代码启动,其功能类似于最小化的操作系统。统一可扩展固件接口(UEFI)被定义为操作系统与平台固件之间的软件接口,实现了系统初始化与管理的标准化。作为UEFI的重要开源实现,EFI开发套件II(EDK2)在塑造固件架构方面发挥着关键作用。尽管已获广泛采用,该架构仍面临早期系统资源受限及缺乏标准安全功能等挑战。此外,专门用于固件分析的开源工具稀缺,凸显了对适应性创新解决方案的需求。本文探讨通用代码审计工具在固件分析中的应用,特别聚焦于EDK2平台。尽管这些工具最初并非为固件分析设计,但实践证明其在识别固件安全关键改进领域方面具有显著效果。我们通过在EDK2上部署核心审计工具获得的研究成果,依据方法论对这些工具进行分类,并阐明其揭示独特固件属性的能力,为固件安全性的理解与提升作出重要贡献。