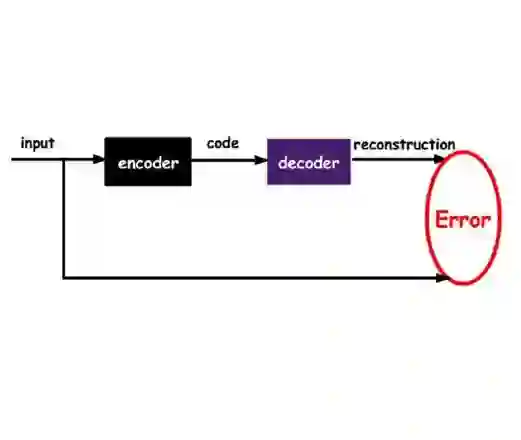
The IEC 61850 Generic Object-Oriented Substation Event (GOOSE) protocol plays a critical role in real-time protection and automation of digital substations, yet its lack of native security mechanisms can expose power systems to sophisticated cyberattacks. Traditional rule-based and supervised intrusion detection techniques struggle to detect protocol-compliant and zero-day attacks under significant class imbalance and limited availability of labeled data. This paper proposes an explainable, unsupervised multi-view anomaly detection framework for IEC 61850 GOOSE networks that explicitly separates semantic integrity and temporal availability. The approach employs asymmetric autoencoders trained only on real operational GOOSE traffic to learn distinct latent representations of sequence-based protocol semantics and timing-related transmission dynamics in normal traffic. Anomaly detection is implemented using reconstruction errors mixed with statistically grounded thresholds, enabling robust detection without specified attack types. Feature-level reconstruction analysis provides intrinsic explainability by directly linking detection outcomes to IEC 61850 protocol characteristics. The proposed framework is evaluated using real substation traffic for training and a public dataset containing normal traffic and message suppression, data manipulation, and denial-of-service attacks for testing. Experimental results show attack detection rates above 99% with false positives remaining below 5% of total traffic, demonstrating strong generalization across environments and effective operation under extreme class imbalance and interpretable anomaly attribution.
翻译:IEC 61850面向对象的通用变电站事件(GOOSE)协议在数字化变电站的实时保护与自动化中起着至关重要的作用,但其缺乏原生安全机制的特性可能使电力系统暴露于复杂的网络攻击之下。在显著的类别不平衡和标记数据可用性有限的条件下,传统的基于规则和有监督的入侵检测技术难以检测协议合规及零日攻击。本文提出了一种用于IEC 61850 GOOSE网络的可解释、无监督多视图异常检测框架,该框架明确分离了语义完整性与时间可用性。该方法采用非对称自编码器,仅使用真实运行的GOOSE流量进行训练,以学习正常流量中基于序列的协议语义和与时间相关的传输动态的独特潜在表示。异常检测通过结合重建误差与基于统计的阈值来实现,从而能够在无需指定攻击类型的情况下进行鲁棒检测。特征级重建分析通过直接将检测结果与IEC 61850协议特征相关联,提供了内在的可解释性。所提出的框架使用真实变电站流量进行训练,并采用一个包含正常流量以及消息抑制、数据篡改和拒绝服务攻击的公共数据集进行测试。实验结果显示,攻击检测率超过99%,误报率保持在总流量的5%以下,证明了该框架在不同环境下的强泛化能力,以及在极端类别不平衡条件下的有效运行和可解释的异常归因能力。