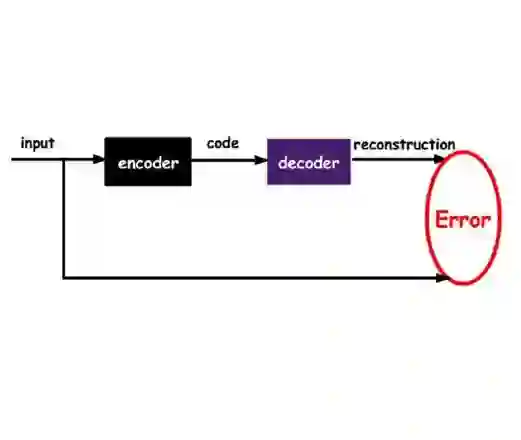
This study investigates the vulnerabilities of data-driven offline signature verification (DASV) systems to generative attacks and proposes robust countermeasures. Specifically, we explore the efficacy of Variational Autoencoders (VAEs) and Conditional Generative Adversarial Networks (CGANs) in creating deceptive signatures that challenge DASV systems. Using the Structural Similarity Index (SSIM) to evaluate the quality of forged signatures, we assess their impact on DASV systems built with Xception, ResNet152V2, and DenseNet201 architectures. Initial results showed False Accept Rates (FARs) ranging from 0% to 5.47% across all models and datasets. However, exposure to synthetic signatures significantly increased FARs, with rates ranging from 19.12% to 61.64%. The proposed countermeasure, i.e., retraining the models with real + synthetic datasets, was very effective, reducing FARs between 0% and 0.99%. These findings emphasize the necessity of investigating vulnerabilities in security systems like DASV and reinforce the role of generative methods in enhancing the security of data-driven systems.
翻译:本研究探讨了数据驱动离线签名验证(DASV)系统面对生成式攻击的脆弱性,并提出了鲁棒的对抗措施。具体而言,我们探究了变分自编码器(VAEs)和条件生成对抗网络(CGANs)在生成挑战DASV系统的欺骗性签名方面的有效性。我们使用结构相似性指数(SSIM)评估伪造签名的质量,并评估了它们对基于Xception、ResNet152V2和DenseNet201架构构建的DASV系统的影响。初步结果显示,在所有模型和数据集上,错误接受率(FARs)介于0%到5.47%之间。然而,暴露于合成签名后,FARs显著增加,比率范围从19.12%到61.64%。所提出的对抗措施,即使用真实+合成数据集重新训练模型,非常有效,将FARs降低至0%到0.99%之间。这些发现强调了研究如DASV等安全系统漏洞的必要性,并强化了生成式方法在增强数据驱动系统安全性方面的作用。