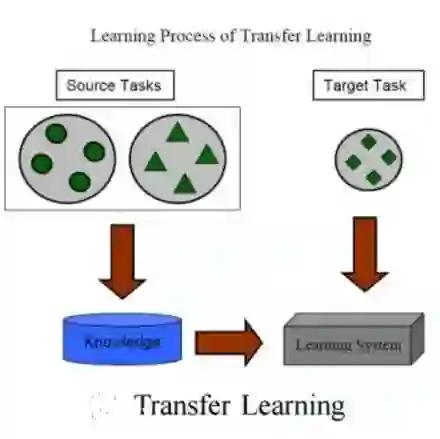
In the current cybersecurity landscape, protecting military devices such as communication and battlefield management systems against sophisticated cyber attacks is crucial. Malware exploits vulnerabilities through stealth methods, often evading traditional detection mechanisms such as software signatures. The application of ML/DL in vulnerability detection has been extensively explored in the literature. However, current ML/DL vulnerability detection methods struggle with understanding the context and intent behind complex attacks. Integrating large language models (LLMs) with system call analysis offers a promising approach to enhance malware detection. This work presents a novel framework leveraging LLMs to classify malware based on system call data. The framework uses transfer learning to adapt pre-trained LLMs for malware detection. By retraining LLMs on a dataset of benign and malicious system calls, the models are refined to detect signs of malware activity. Experiments with a dataset of over 1TB of system calls demonstrate that models with larger context sizes, such as BigBird and Longformer, achieve superior accuracy and F1-Score of approximately 0.86. The results highlight the importance of context size in improving detection rates and underscore the trade-offs between computational complexity and performance. This approach shows significant potential for real-time detection in high-stakes environments, offering a robust solution to evolving cyber threats.
翻译:在当前网络安全形势下,保护通信系统、战场管理系统等军事设备免受复杂网络攻击至关重要。恶意软件通过隐蔽手段利用漏洞,往往能够规避软件签名等传统检测机制。机器学习/深度学习在漏洞检测中的应用已在文献中得到广泛研究,然而现有检测方法在理解复杂攻击的上下文和意图方面存在不足。将大语言模型与系统调用分析相结合,为增强恶意软件检测提供了一种有前景的方法。本文提出了一种创新框架,利用大语言模型基于系统调用数据进行恶意软件分类。该框架采用迁移学习技术,对预训练的大语言模型进行适配以完成恶意软件检测任务。通过在良性和恶意系统调用数据集上重新训练,模型被优化以识别恶意软件活动特征。基于超过1TB系统调用数据集的实验表明,BigBird和Longformer等具有更大上下文窗口的模型实现了约0.86的准确率和F1分数。研究结果凸显了上下文规模对提升检测率的重要性,并揭示了计算复杂度与性能之间的权衡关系。该方法在高风险环境下的实时检测中展现出显著潜力,为应对不断演变的网络威胁提供了鲁棒解决方案。