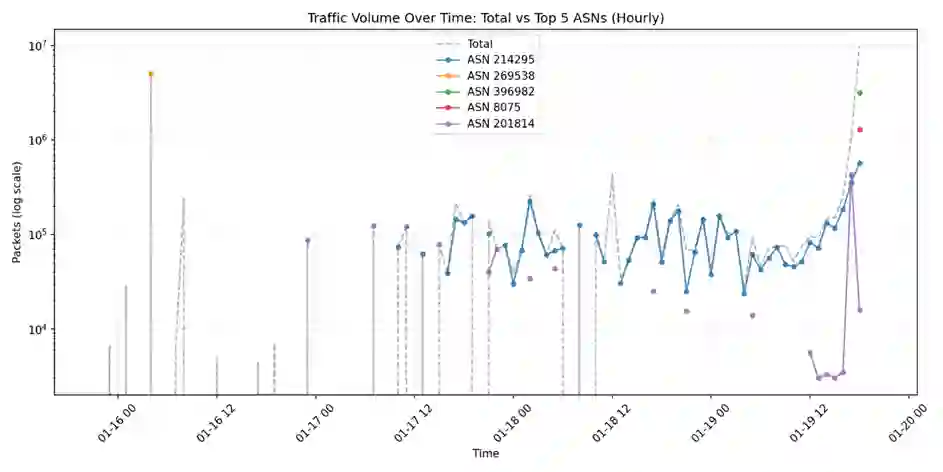
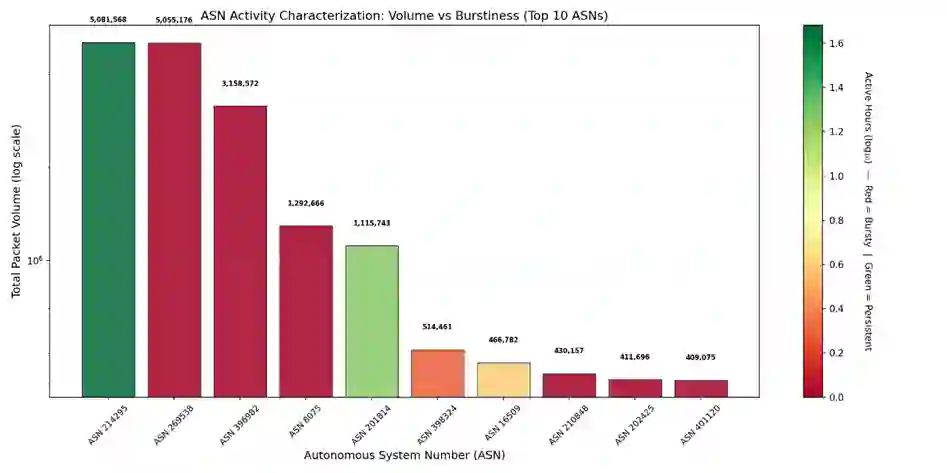
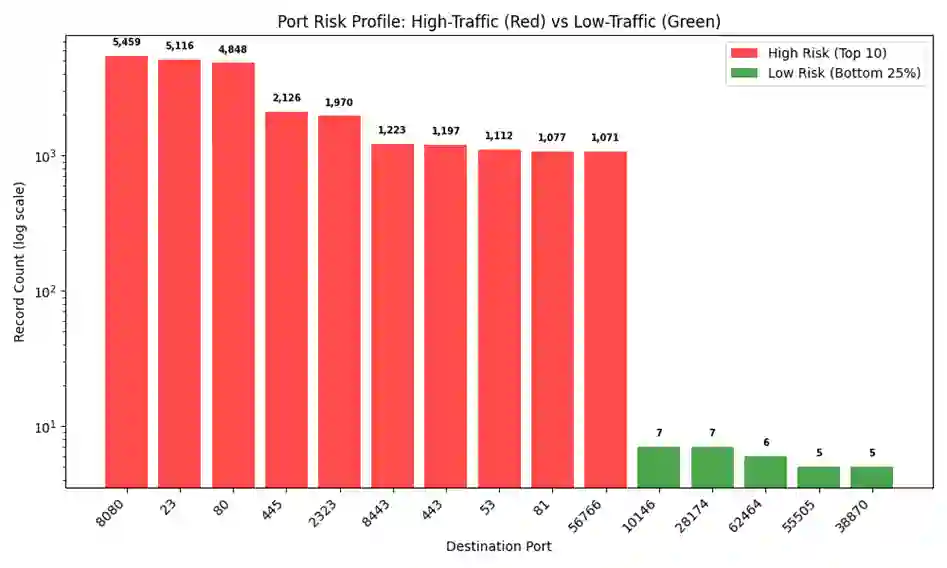
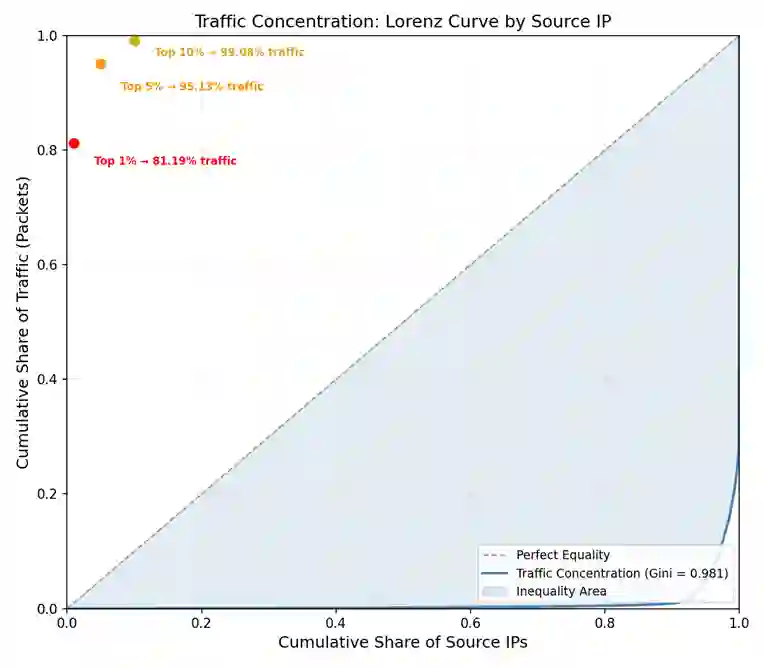
Network telescopes serve as a critical passive monitoring tool for capturing unsolicited Internet traffic, providing insights into global scanning and reconnaissance behavior. This study analyzes a 10-day dataset during January 2025 consisting of approximately 22 million packets collected by the ORION network telescope at Merit Network. By employing privacy-preserving metadata analysis and lightweight behavioral heuristics, we identify scanning and backscatter patterns without payload inspection. Our results reveal a highly structured and centralized ecosystem, where the top 1% of source IP addresses generate over 81% of total traffic. A significant finding is the dominance of Port 23 (Telnet) and Port 2323 (Telnet Alt), which highlights the persistent nature of IoT security threats and widespread attempts to exploit weak credentials in legacy IoT devices. Furthermore, synchronized surges in packet volume and Shannon entropy indicate coordinated, multi-vector reconnaissance campaigns. These findings offer a practical framework for identifying large-scale threat activity and support cybersecurity research and education.
翻译:暂无翻译