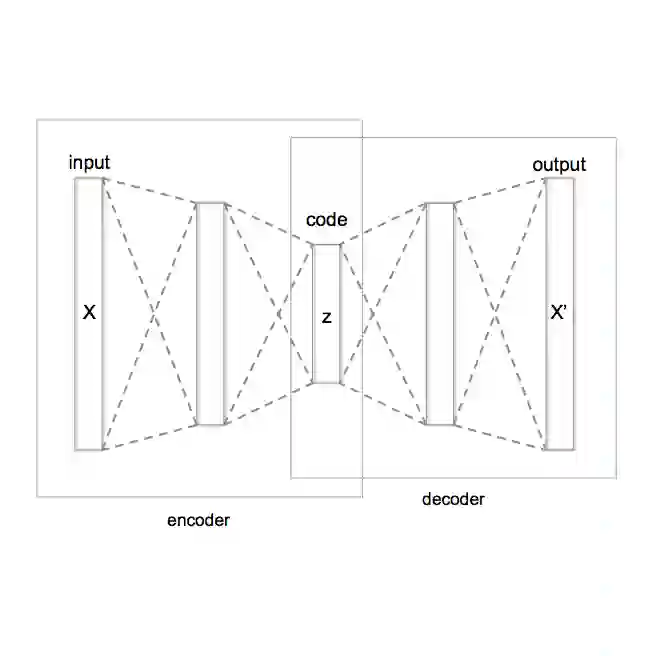
In predictive process monitoring, predictive models are vulnerable to adversarial attacks, where input perturbations can lead to incorrect predictions. Unlike in computer vision, where these perturbations are designed to be imperceptible to the human eye, the generation of adversarial examples in predictive process monitoring poses unique challenges. Minor changes to the activity sequences can create improbable or even impossible scenarios to occur due to underlying constraints such as regulatory rules or process constraints. To address this, we focus on generating realistic adversarial examples tailored to the business process context, in contrast to the imperceptible, pixel-level changes commonly seen in computer vision adversarial attacks. This paper introduces two novel latent space attacks, which generate adversaries by adding noise to the latent space representation of the input data, rather than directly modifying the input attributes. These latent space methods are domain-agnostic and do not rely on process-specific knowledge, as we restrict the generation of adversarial examples to the learned class-specific data distributions by directly perturbing the latent space representation of the business process executions. We evaluate these two latent space methods with six other adversarial attacking methods on eleven real-life event logs and four predictive models. The first three attacking methods directly permute the activities of the historically observed business process executions. The fourth method constrains the adversarial examples to lie within the same data distribution as the original instances, by projecting the adversarial examples to the original data distribution.
翻译:在预测性过程监控中,预测模型易受对抗攻击的影响,输入扰动可能导致错误预测。与计算机视觉领域设计对人类视觉不可察觉的扰动不同,预测性过程监控中对抗样本的生成面临独特挑战。对活动序列的微小改动可能因监管规则或流程约束等底层限制,产生现实中不可能发生的场景。为此,我们专注于生成适应业务流程场景的逼真对抗样本,而非计算机视觉对抗攻击中常见的不可察觉像素级修改。本文提出两种新颖的潜在空间攻击方法,通过向输入数据的潜在空间表示添加噪声生成对抗样本,而非直接修改输入属性。这些潜在空间方法具有领域无关性,且不依赖特定流程知识——我们通过直接扰动业务流程执行的潜在空间表示,将对抗样本的生成限制在已学习的类特定数据分布内。我们在十一个真实事件日志和四个预测模型上,将这两种潜在空间方法与六种其他对抗攻击方法进行比较评估。前三种攻击方法直接置换历史观测业务流程执行中的活动序列。第四种方法通过将对抗样本投影至原始数据分布,约束其必须处于与原始实例相同的数据分布范围内。