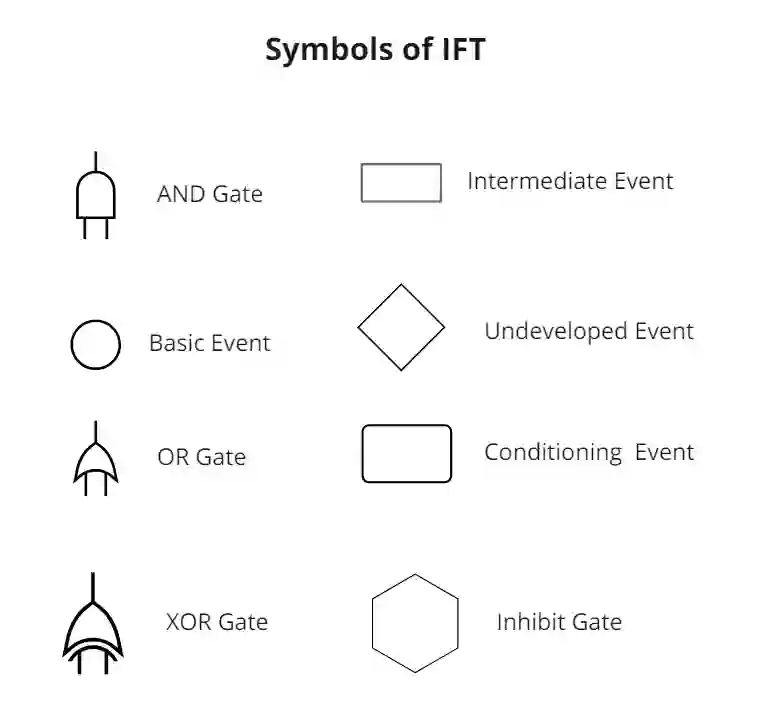
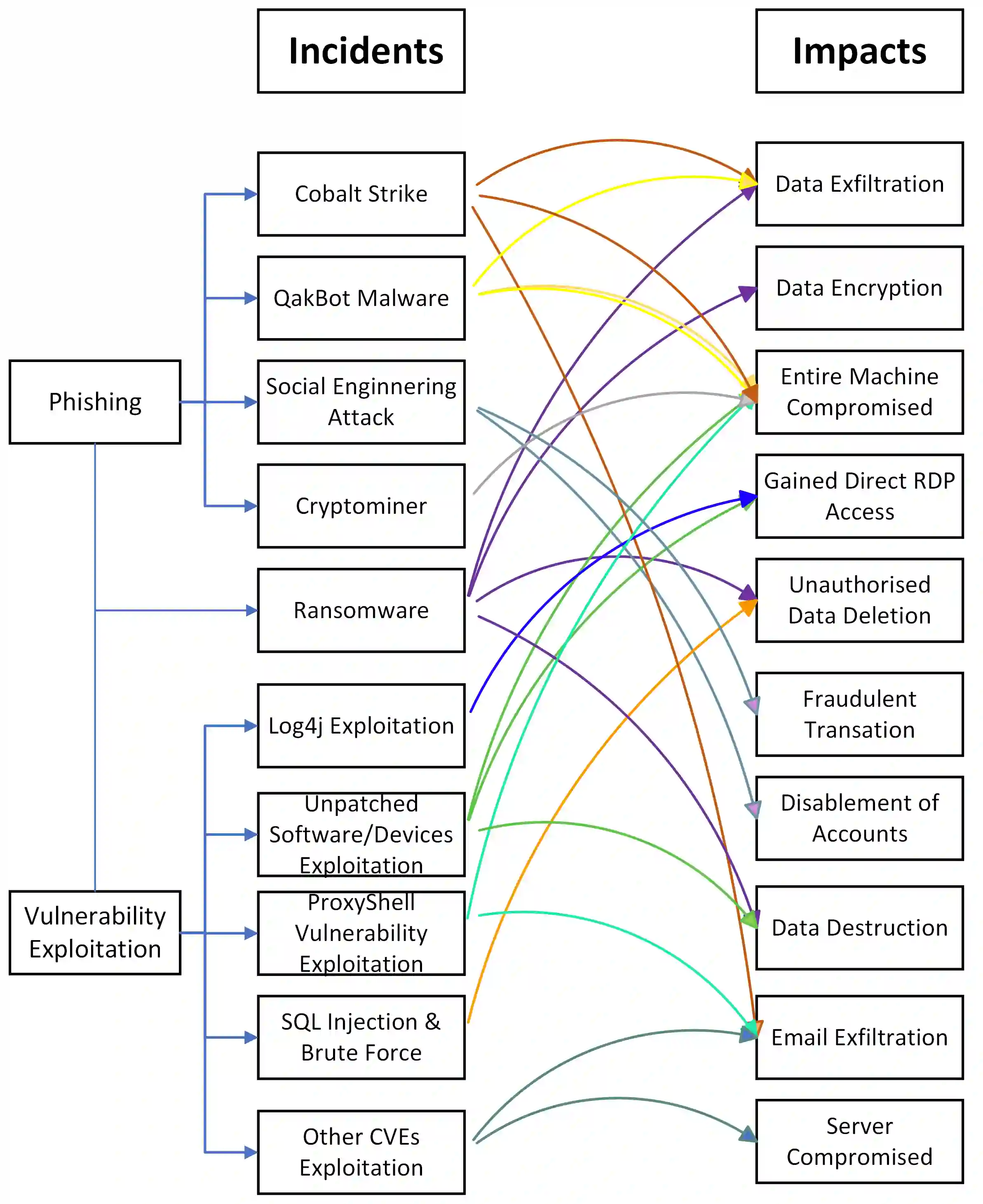
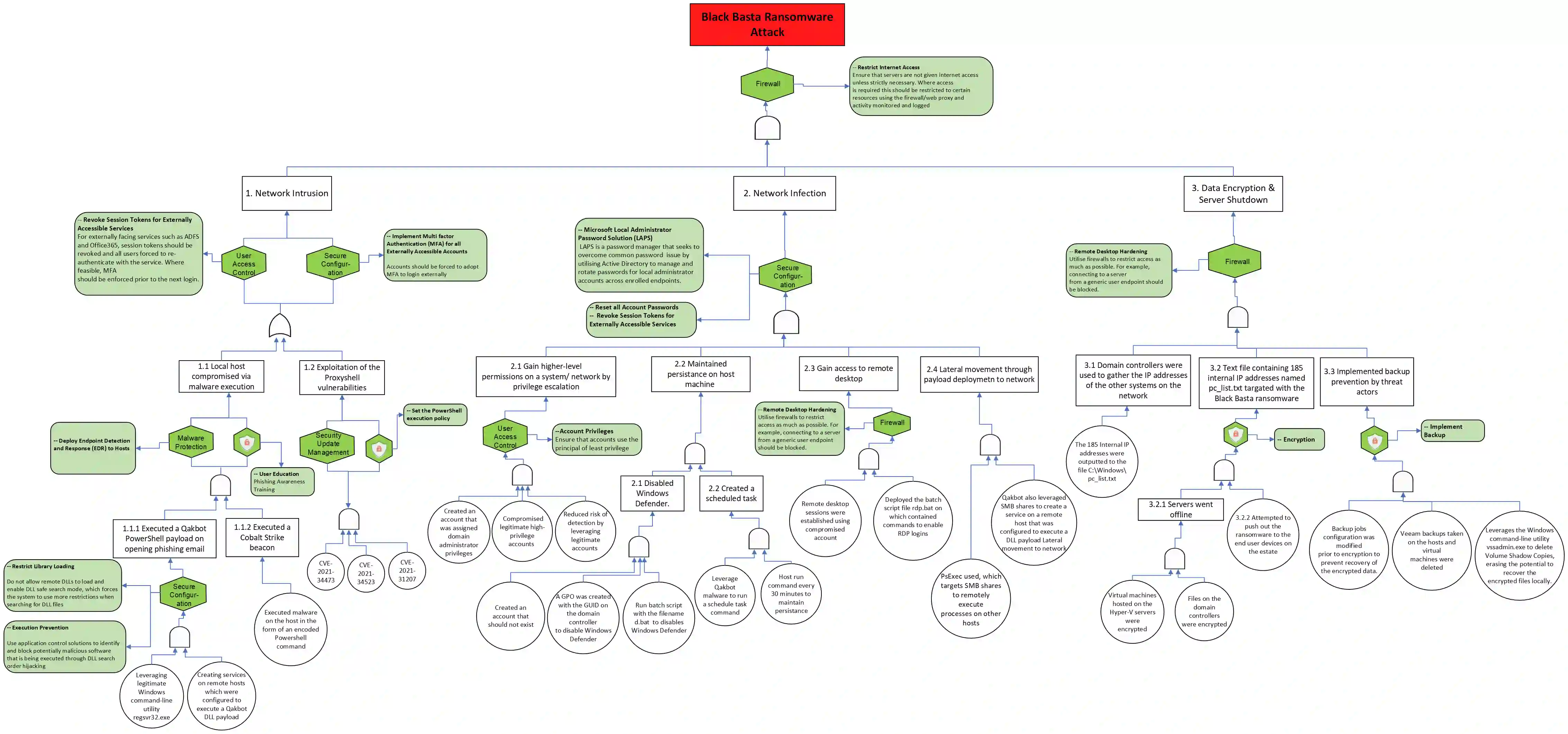
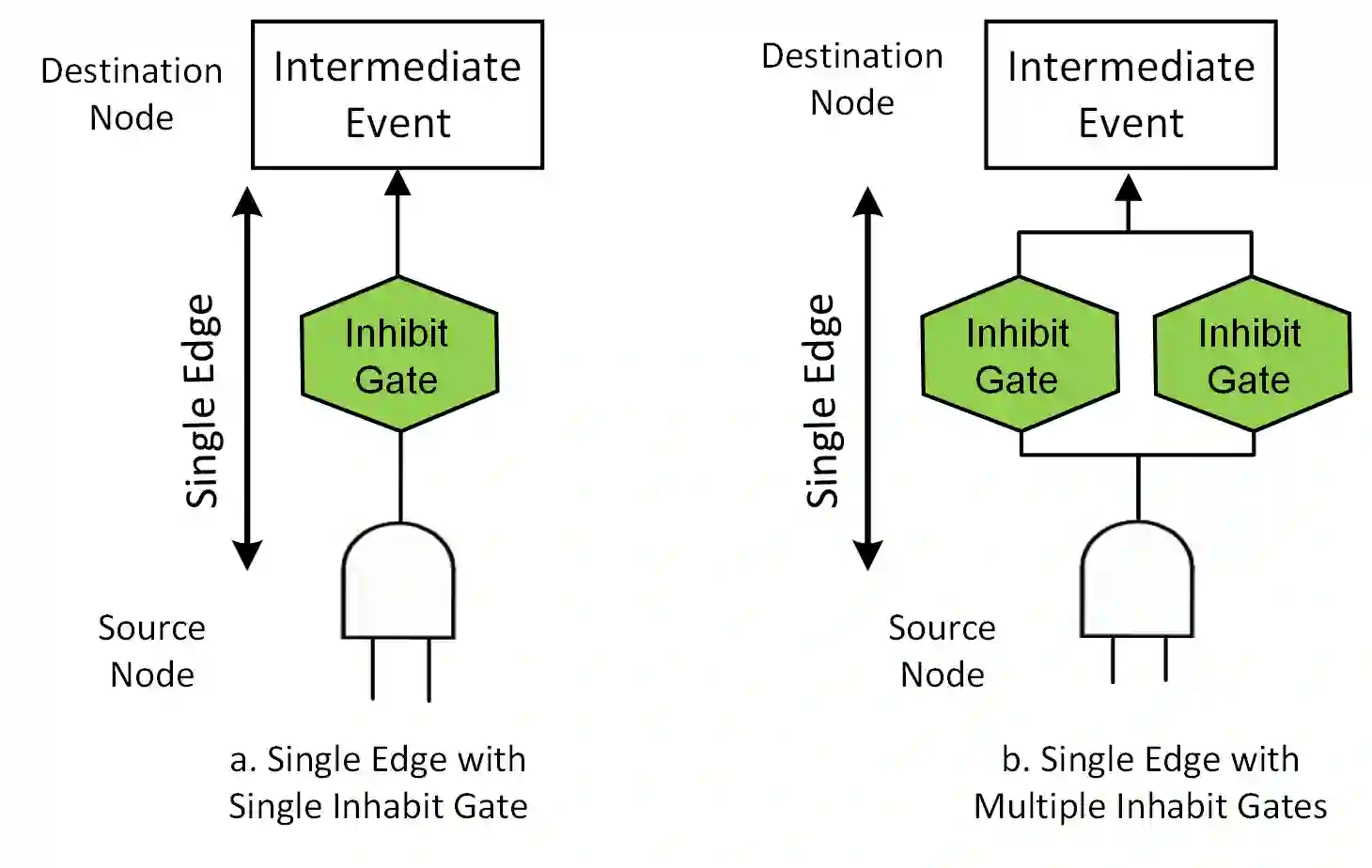
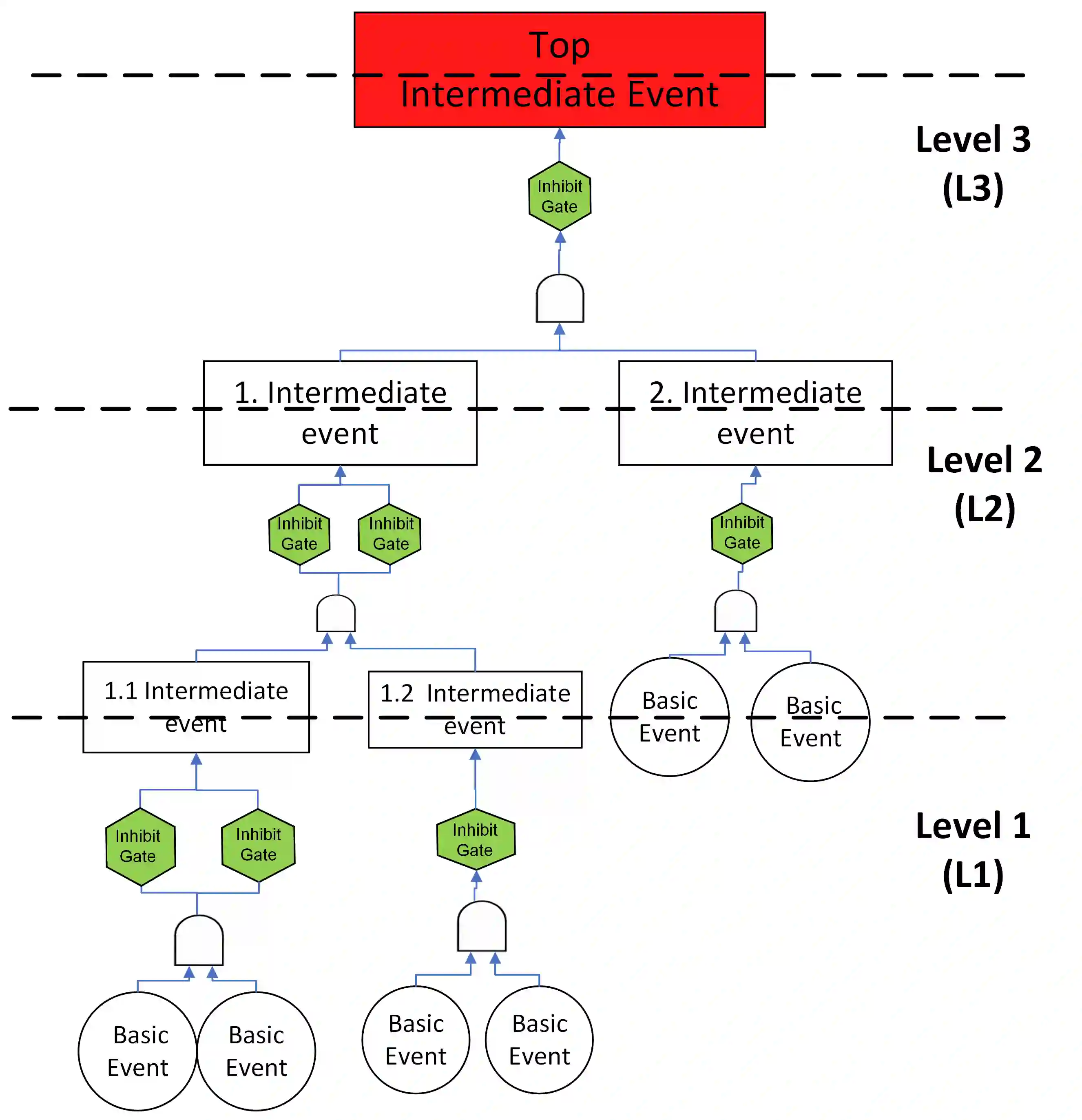
Cyber Essentials (CE) comprise a set of controls designed to protect organisations, irrespective of their size, against cyber attacks. The controls are firewalls, secure configuration, user access control, malware protection & security update management. In this work, we explore the extent to which CE remains robust against an ever-evolving threat landscape. To that end, we reconstruct 45 breaches mapped to MiTRE ATT&CK using an Incident Fault Tree ( IFT ) approach. Our method reveals the intersections where the placement of controls could have protected organisations. Then we identify appropriate Cyber Essential controls and/or Additional Controls for these vulnerable intersections. Our results show that CE controls can effectively protect against most attacks during the initial attack phase. However, they may need to be complemented with additional Controls if the attack proceeds further into organisational systems & networks. The Additional Controls (AC) we identify include back-ups, security awareness, logging and monitoring. Our analysis brings to the fore a foundational issue as to whether controls should exclude recovery and focus only on pre-emption. The latter makes the strong assumption that a prior identification of all controls in a dynamic threat landscape is indeed possible. Furthermore, any potential broadening of technical controls entails re-scoping the skills that are required for a Cyber Essentials (CE) assessor. To that end, we suggest human factors and security operations and incident management as two potential knowledge areas from Cyber Security Body of Knowledge (CyBOK) if there is any broadening of CE based on these findings.
翻译:网络基础(CE)包含一系列旨在保护各类规模组织免受网络攻击的控制措施。这些控制措施涵盖防火墙、安全配置、用户访问控制、恶意软件防护及安全更新管理。本研究探讨了在不断演变的威胁环境中,网络基础控制措施在多大程度上仍能保持其有效性。为此,我们采用事故故障树(IFT)方法重构了45起映射到MITRE ATT&CK框架的安全漏洞事件。我们的方法揭示了控制措施部署本可保护组织的关键节点。随后,我们为这些脆弱节点识别了适用的网络基础控制措施和/或补充控制措施。研究结果表明,网络基础控制措施在攻击初始阶段能有效防御大多数攻击。然而,若攻击进一步渗透至组织系统与网络内部,则可能需要补充控制措施予以增强。我们识别的补充控制措施(AC)包括数据备份、安全意识培训、日志记录与监控。我们的分析揭示了一个根本性问题:控制措施是否应排除恢复机制而仅专注于预防?后一种做法强烈假设在动态威胁环境中预先识别所有控制措施确实是可行的。此外,任何对技术控制措施的潜在扩展都需要重新界定网络基础(CE)评估员所需的技能范围。基于此,我们建议若根据这些发现扩展网络基础控制范围,可考虑从网络安全知识体系(CyBOK)中引入人因安全、安全运营与事件管理这两个潜在知识领域。