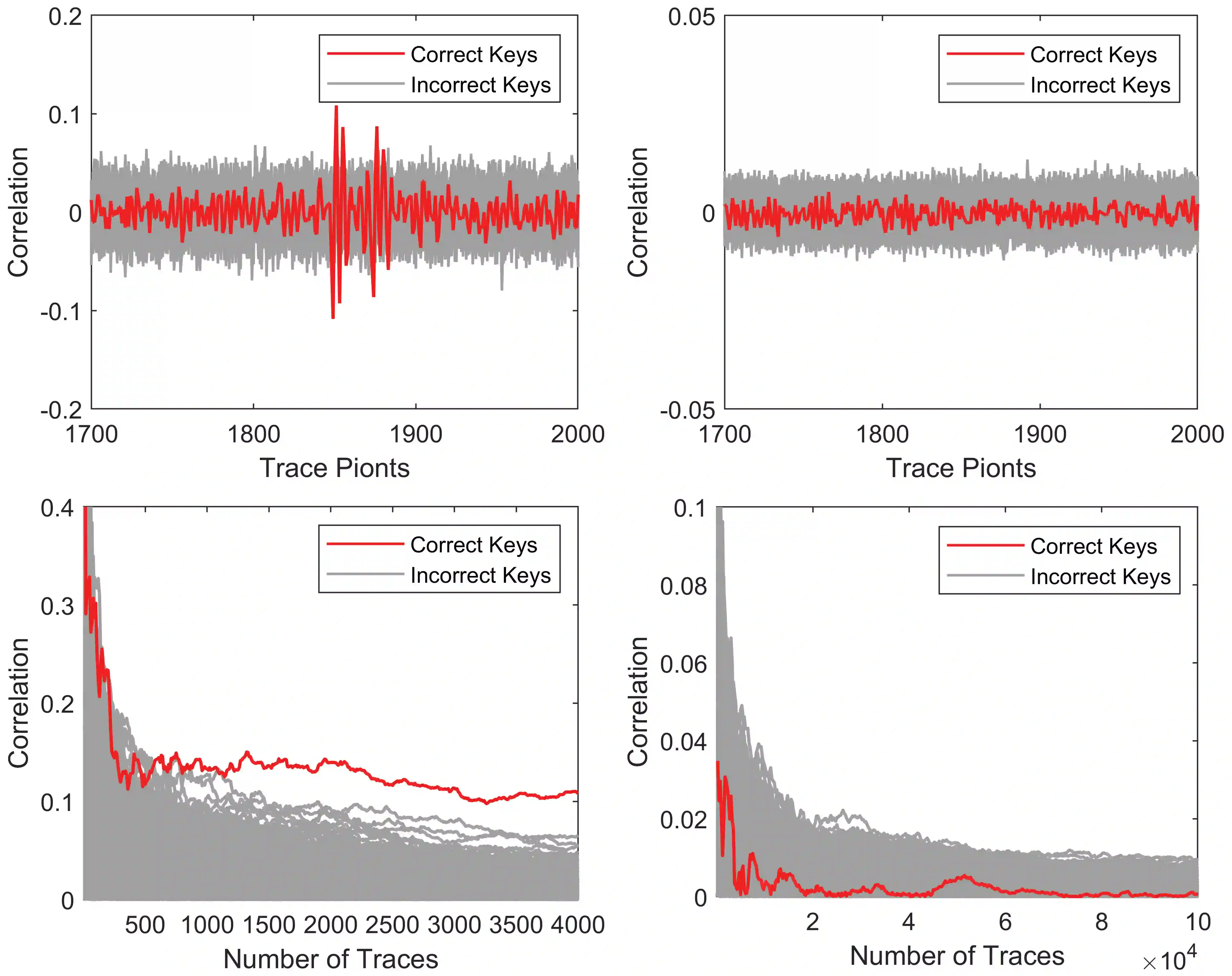
CRYSTALS-Kyber (a.k.a. Kyber) has been drafted to be standardized as the only key encapsulation mechanism (KEM) scheme by the national institute of standards and technology (NIST) to withstand attacks by large-scale quantum computers. However, the side-channel attack (SCA) on its implementation is still needed to be well considered for the upcoming migration. In this brief, we propose a secure and efficient hardware implementation for Kyber by incorporating a novel compact shuffling architecture. First of all, we modify the Fisher-Yates shuffle to make it more hardware-friendly. We then design an optimized shuffling architecture for the well-known open-source Kyber hardware implementation to enhance the security of all the potential side-channel leakage points. Finally, we implement the modified Kyber design on FPGA and evaluate its security and performance. The security is verified by conducting the correlation power analysis (CPA) attacks on the hardware. Meanwhile, FPGA place-and-route results show that the proposed design reports only 8.7% degradation on the hardware efficiency compared with the original unprotected version, much better than existing hiding schemes.
翻译:CRYSTALS-Kyber(简称Kyber)已被美国国家标准与技术研究院(NIST)选定为唯一将标准化的密钥封装机制(KEM)方案,旨在抵御大规模量子计算机的攻击。然而,在即将到来的迁移过程中,其实施过程中的侧信道攻击(SCA)防护仍需充分考虑。本文提出一种通过引入新型紧凑乱序架构来实现Kyber安全高效硬件实施的方案。首先,我们改进Fisher-Yates乱序算法以提升其硬件友好性。随后针对知名的开源Kyber硬件实现,设计优化的乱序架构以增强所有潜在侧信道泄漏点的安全性。最后,我们在FPGA上实现改进后的Kyber设计并评估其安全性与性能。通过执行相关性功耗分析(CPA)攻击验证了硬件安全性。同时,FPGA布局布线结果表明,相较于原始无防护版本,所提方案的硬件效率仅降低8.7%,远优于现有掩蔽方案。