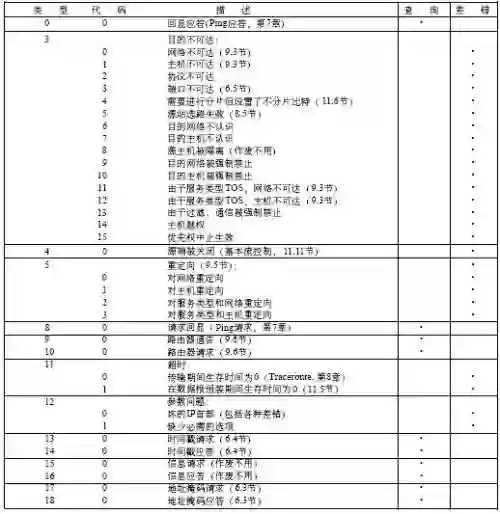
Passive measurement has traditionally focused on inbound traffic to detect malicious activity, based on the assumption that threats originate externally. In this paper, we offer a complementary perspective by examining outbound traffic, and argue that a narrow subset -- what we term erroneous outbound traffic -- is a lighter and revealing yet overlooked data source for identifying a broad range of security threats and network problems. This traffic consists of packets sent by internal hosts that either receive no response, trigger ICMP errors, or are ICMP error messages themselves generated in response to unsolicited requests. To demonstrate its potential, we collect and analyse erroneous traffic from a large network, uncovering a variety of previously unnoticed issues, including misconfigurations, obsolete deployments and compromised hosts.
翻译:传统被动测量通常聚焦于入站流量以检测恶意活动,其基本假设是威胁源自外部。本文通过考察出站流量提供了一个互补视角,并论证一个狭窄的子集——我们称之为异常出站流量——是识别广泛安全威胁与网络问题的一种更轻量化、更具揭示性却长期被忽视的数据源。该流量由内部主机发送的数据包构成,这些数据包要么未收到任何响应,要么触发了ICMP错误,要么本身就是响应非请求报文而产生的ICMP错误消息。为验证其潜力,我们收集并分析了来自大型网络的异常流量,发现了多种先前未被注意的问题,包括配置错误、过时部署及受感染主机。