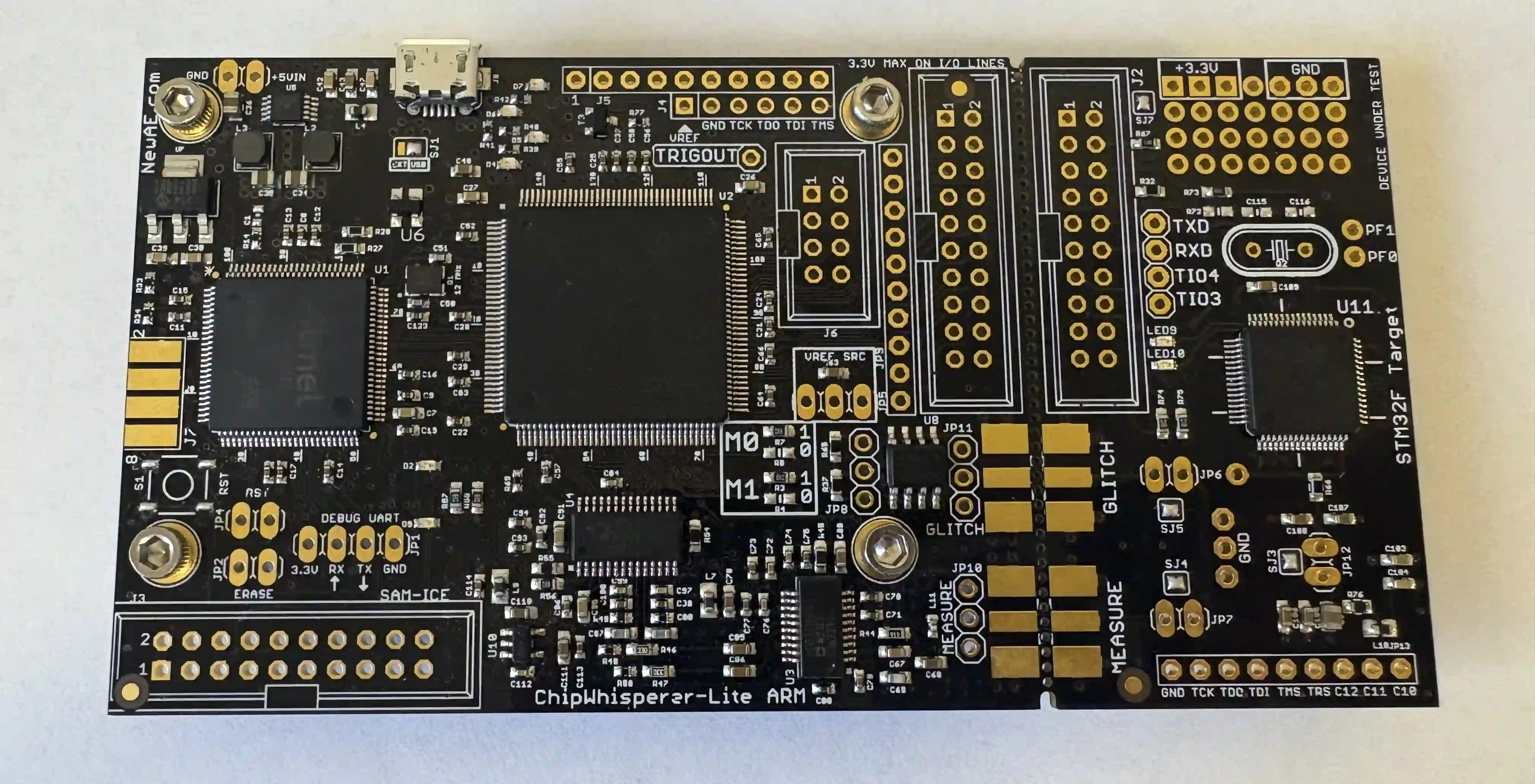
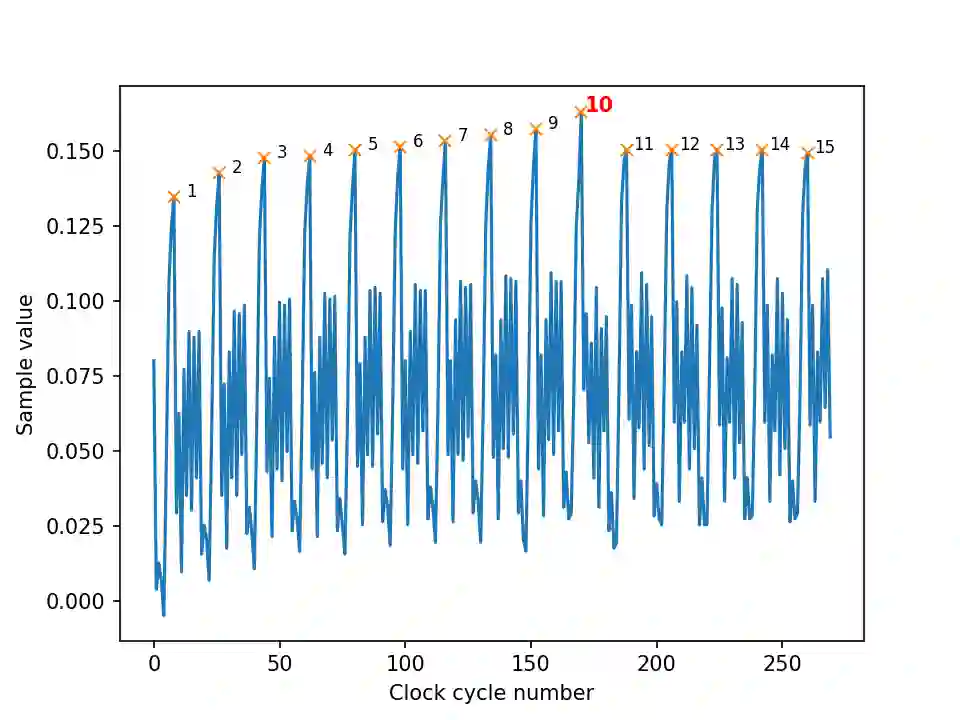
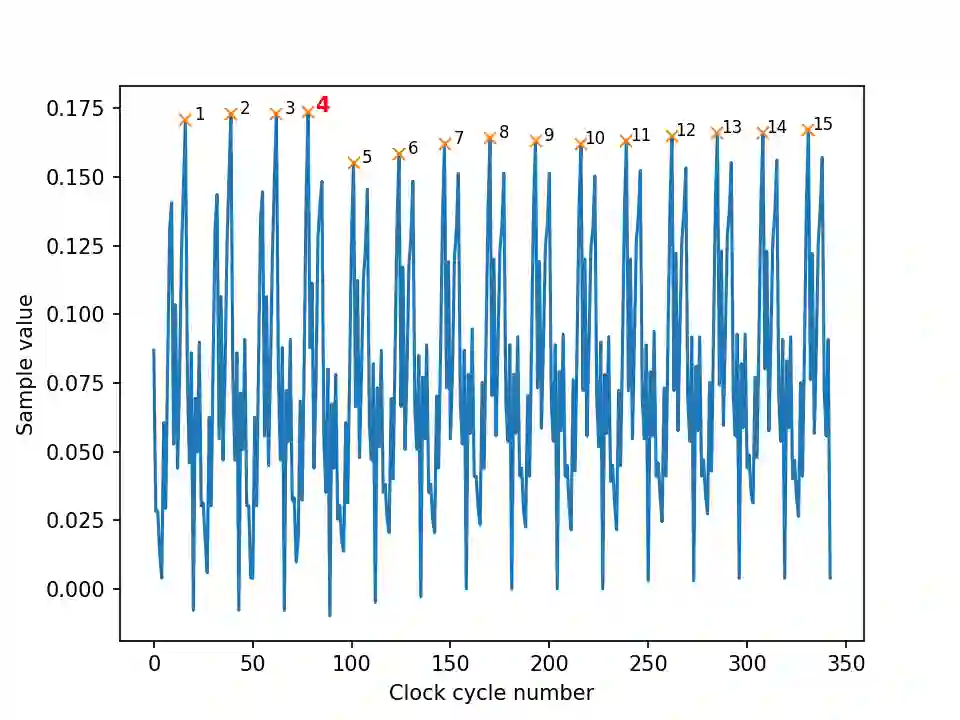
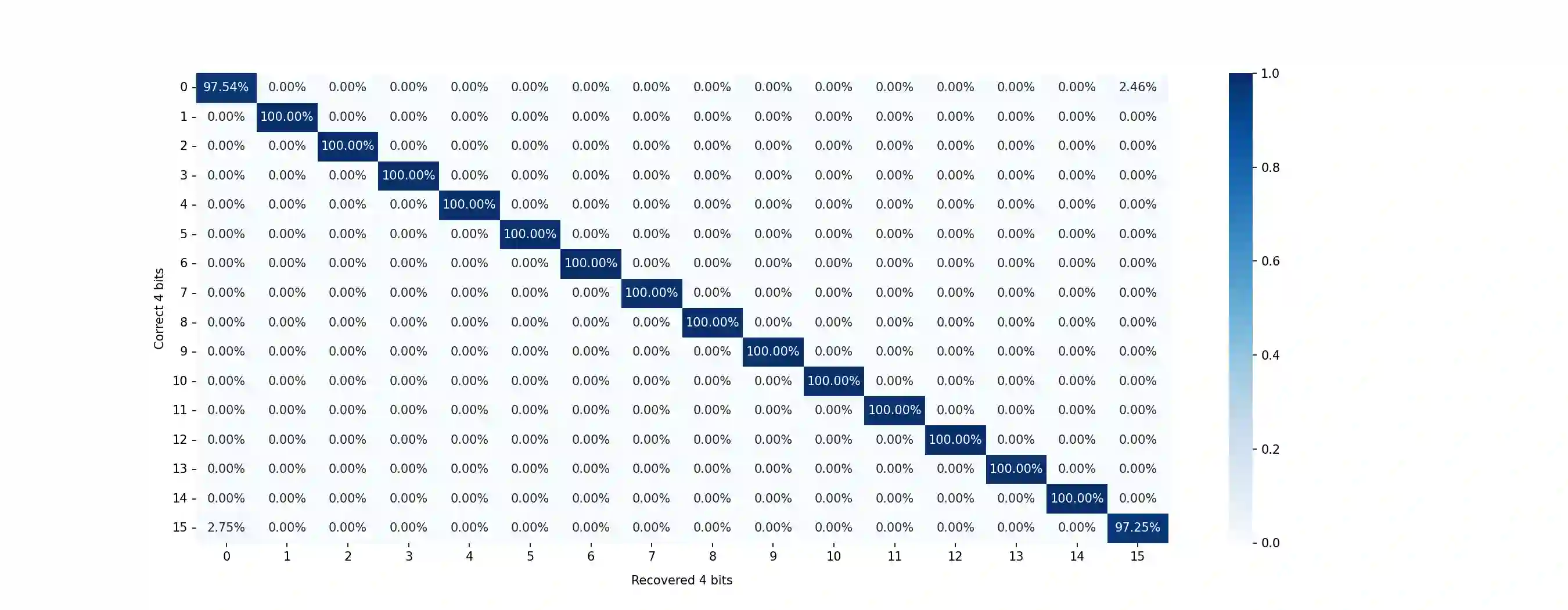
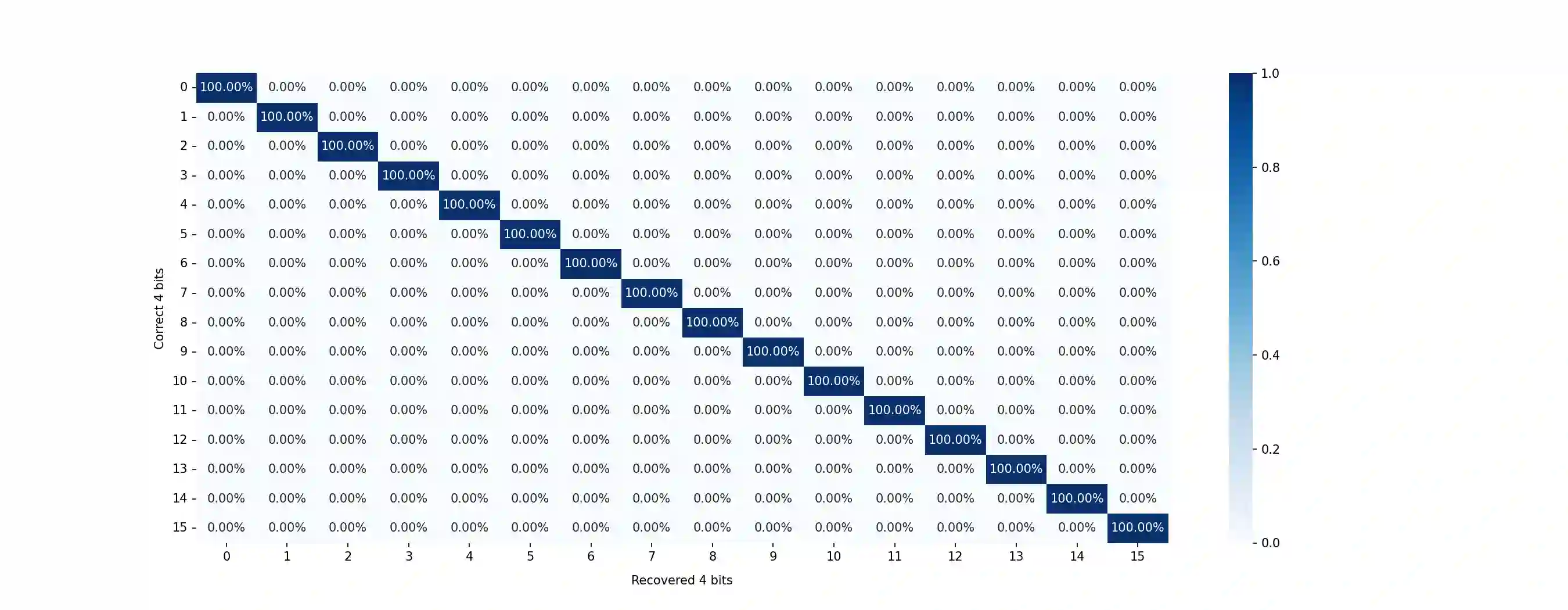
The Hamming Quasi-Cyclic (HQC) cryptosystem was selected for standardization in the fourth round of the NIST Post-Quantum Cryptography (PQC) standardization project. The goal of the PQC project is to standardize one or more quantum-resistant public-key cryptographic algorithms. In this paper, we present a single-trace Simple Power Analysis (SPA) attack against HQC that exploits power consumption leakage that occurs during polynomial multiplication performed at the beginning of HQC decryption. Using the ChipWhisperer-Lite board, we perform and evaluate the attack, achieving a 99.69% success rate over 10 000 attack attempts. We also propose various countermeasures against the attack and evaluate their time complexity.
翻译:汉明准循环(HQC)密码系统在NIST后量子密码(PQC)标准化项目的第四轮中被选为标准。PQC项目的目标是标准化一个或多个抗量子公钥密码算法。本文提出了一种针对HQC的单迹线简单功耗分析(SPA)攻击,该攻击利用了HQC解密开始时执行多项式乘法期间发生的功耗泄漏。利用ChipWhisperer-Lite开发板,我们执行并评估了该攻击,在10,000次攻击尝试中实现了99.69%的成功率。我们还提出了针对该攻击的各种防护措施,并评估了其时间复杂度。